Elias Augusto
Cross posted from my Medium under @eaugusto
I want to preface this article by saying that if you’re like me, new to malware analysis and on a budget, studying without access to course materials may not be the best option for you. The best way to pursue the SANS GREM certification without a source of funding for the course is to apply for the SANS Work Study program for the FOR610 course. In exchange for assisting the course instructor, you will be allowed to evaluate the course and attempt the certification exam. You will also be provided copies of the books and course materials, which cannot be acquired any other way due to SANS policy on sharing of course materials. The total cost of this program is actually lower than what I paid out of pocket for just the exam.
https://www.sans.org/work-study/
To participate in the Work Study program, however, your application must be accepted, and you must be able to attend a SANS conference for 6 days. I did not pursue this option because the SANS conferences in my area conflicted with other important items on my schedule. I also did not think it appropriate to ask my employer to cover the cost of the course, as it was not directly related to my project role. For these reasons, SANS training was out of the question.
Now that I’ve established why I did what I did, let’s get into the “how”.
What I Needed to learn
Straight from the SANS website, for the GREM I needed:
- Windows assembly concepts for reverse engineering — What you do in IDA Pro, why you need assembly and C knowledge
- Common characteristics of Windows Malware — API functions, threads, structures
- In-depth analysis of malicious and protected executables — What you do in IDA Pro after some practice
- Malicious document analysis — Attackers put scripts in files
- Malicious web browser script analysis —Attackers put scripts on the internet, command and control traffic flows over the wire
- Memory forensics — Volatility
The Importance of Assembly Language and C
Before I get into the different resources I used to prepare to the exam, I want to note that it’s vital to have at least a shaky grasp on x86 assembly. You really can’t reverse engineer a portable executable or shellcode without it. This really isn’t as bad as it seems, assembly at it’s core is just arithmetic that makes computers do things. All you need to know to begin learning binary reverse engineering is the x86 registers, variable types (word, dword, int, char, etc.), stack basics, and some program flow instructions. Here’s a resource I found helpful for learning the basics:
https://www.tutorialspoint.com/assembly_programming/
A working knowledge of C is important, but you’ll know most of what you need if you know how to program in a C like language such as Java. The only new concepts you’ll need for malware reverse engineering are pointers, memory allocation, and the heap. I learned what I needed through these two resources:
https://www.tutorialspoint.com/cprogramming/index.htm
Reverse Engineering “Reverse Engineering”
I decided to title this article “Grey Box Testing” because looking back, I realized that that was basically what I did to study for this exam. As someone who was new to malware analysis, I knew little of what to expect. Throughout my preparation for the exam, I referred to these sources of information:
- Book recommendations posted by those who passed the exam without paying for the course three to five years ago
- The SANS FOR610 official course syllabus
- Malicious file analysis cheat sheets created by Lenny Zeltser
I’ll break these items down into sections to show what I learned from each source.
Book Recommendations
Picking useful books is very important to GREM success, as you’re allowed to take an armful of them into GIAC exams as references. Most GREM certification holders will gladly share a list of the (non-SANS) books that they used to prepare with people wondering where to start studying for the exam. My first step was looking at the recommended reading lists of as many GREM alumni I could find. The books I found most consistently recommended were:
- “Practical Malware Analysis”— A fantastic guide to behavioral analysis, reverse engineering, and defeating anti-analysis. This book is non-negotiable, you won’t find a source that doesn’t recommend it. In addition to the information, it comes with very helpful labs to reinforce your knowledge.
- “The Malware Analyst’s Cookbook” — A guide to a large variety of malware analysis tools. The labs and scripts are very outdated, but the tool overviews were very useful. I used the sections on memory forensics, browser script malware, and malicious document analysis to prepare for my exam.
- “The Art of Memory Forensics” — It’s helpful to have this not necessarily as a primary resource, but as a supplementary resource to the “Malware Analyt’s Cookbook” section on memory forensics. Many of the Volatility plugins you’ll need aren’t covered in much detail, and information from the MAC should be cross-referenced with information from this book. This book also covers a lot of windows internals that are useful for the exam.
- “Windows Internals 6 or 7” — I personally think that these books are overkill. If you’re familiar with Windows from a security standpoint, the prior books are all you need to understand Windows Internals. I would never recommend taking these books with you into the exam or even indexing it. All relevant information is already in the “Art of Memory Forensics” or on the MSDN website.
- “The IDA Pro Book” — I don’t think anybody will tell you to take this book into the exam, but whether or not you utilize it at all is really a question of how you learn tools. I learned IDA Pro using PMA and some fiddling in my free time, so I didn’t end up needing it. If you learn tools best by reading long books with few images or illustrations, this is the perfect book for you.
The SANS FOR610 Syllabus
This one is pretty simple. The SANS GREM exam is the exam associated with the SANS FOR610 course, so it’s safe to assume that what you learn in the course is what you will apply on the exam. While I didn’t have access to the course, I did have access to the syllabus on the SANS website, an overview of both the topics and tools that the course covered. The FOR610 syllabus was more useful for tools than topics, though this is not true of all SANS DFIR courses. Some seem to list few tools but have a breakdown of every topic. I think it depends on how technical vs. theory based a course is.
The list of tools on the syllabus may not be comprehensive, but it’s the only list you’ll get. Familiarize yourself with every tool on the list, what they look like, how they work, and what they do. I usually start at a tool’s github page and go from there. “The Malware Analyst’s Cookbook” and Lenny Zeltser’s website both have great tool references.
Want to narrow down what you need to know for the exam? If a topic seems a bit broad or a tool too important for the syllabus not to mention, it’s probably not in the course or on the exam.
Lenny Zeltser’s Infosec Cheat Sheets
Lenny Zeltser, one of the SANS FOR610 instructors who helped write both the course and the exam, publishes cheat sheets for topics like reverse engineering malicious code and analyzing malicious documents. These just happen to be some of the same topics referenced in both the FOR610 syllabus and on the GREM webpage. It may be a good idea to study and take notes on the contents of these cheat sheets.
A cheat sheet that may really help you with the “Practical Malware Analysis” labs and x86 assembly calling conventions:
Next Steps: Labs, Special Topics, and Proper Indexing
I recommend following along with the labs in “Practical Malware Analysis” and the memory forensics section of “The Malware Analyst’s Cookbook” as you read through these books. Do a lab a night, a lab every two nights, whatever works best for you. Practice time is flexible, but practice is not optional. Practice is the best way to reinforce understanding of the material, especially when you’re dealing with a lot of tools. The best way to learn tools is to use them. For malicious document forensics, it may be useful to take some Didier Stevens online workshops, as he wrote many of the tools mentioned in the FOR610 syllabus under this section.
http://didierstevenslabs.com/products.html
Between doing all of the labs and indexing, I needed to take a brain break. I decided to pursue a topic that would help me with the exam, but would also take me away from exhausting exam preparation: basic exploit and shellcode writing. I came back refreshed and more motivated than ever after three weeks on this preparation vacation. I recommend finding a fun topic that touches assembly and reverse engineering to learn if you’re feeling exhausted or demotivated.
After you’ve gone over all of the books you’ll be using, done some labs, and taken a brain break, it’s time to prepare for your first practice exam. A lot of people recommend not using an index for your practice exam, but I think that creating an index before attempting a practice exam is essential. Partially because practice exams can be used to tell you where the holes in your index lie, partially because indexing is the best way to review all of the information you learned over what may have been months of studying.
What is an Index?
Along with your reference books, you’re allowed to take notes into the practice exam. Traditionally, most people take an index of all of the books they’ve read into the exam. Indexes are usually created as spreadsheets with filtered columns. I recommend color coding your index. An index should include all important topics, page numbers for each topic, and notes for each topic. My index also included the FOR610 domain I assumed every topic belonged to. In my notes, I highlighted important things such as Windows API functions, structures, and Volatility plugins. Page numbers should also be tabbed in the books you’ll be bringing into the exam. I color coded my tabs to match the index, which was a big help when I needed to look something up fast.

With this exam there will be a lot of topics covered in online resources but none of your books. I like to add notes on these topics to the index with a blank page number. It’s tidier than creating a separate notes sheets for each topic not located in a book.
Note that your index will probably be very different than mine, as you will find a style that suits you best. Never use another person’s index, as this is both a violation of the SANS guidelines and useless as a study aid because it was not made by you. For this same reason, it is usually recommended that those who took the course and have SANS books that include premade indexes create their own instead of using these indexes. Never copy any information into the index directly from a website or word for word from a book. You can do this in a separate notes sheet if you want, but not in your index. This is not a rules violation, just a good rule of thumb. Everything in your index should be in your own words, by your own hand. The act of creating the index is vital to exam preparation.
Any index you create before the first practice exam is going to have holes, especially if you didn’t take the course. Don’t be afraid of going into your first practice exam with a 20 or 30 page index. I came in with a 25 page index, but my index the night before the real exam was over 40 pages long.
Practice Exams
Before I start: ONLY purchase OFFICIAL practice exam attempts from the GIAC website, http://www.giac.org. NEVER use any other source for practice exams. This is prohibited under the GIAC exam guidelines and considered cheating. These unofficial practice exams use stolen, outdated exam questions and are not to be considered a study resource. Purchase official practice exam attempts here:
https://www.giac.org/exams/preparation#practice
Now that that’s out of the way, I recommend that you take a practice exam before purchasing the test. The test comes with two practice exams, but by the time you’re there you’ve spent $2,000 and have no idea whether you’re ready for the exam. Your first practice exam is a great way to find out how far away you are from being able to purchase the exam. If you pass it, I recommend purchasing the exam as soon as possible. If not, it will tell you the areas that you are weak in so that you can focus on these before purchasing the exam.
The first and subsequent practice tests are also a great way to fill in holes in your index. As I mentioned earlier, the FOR610 syllabus is not comprehensive, and practice exams are the only way to find tools and topics that you need to study more. Avoid just writing what you remember about the answers into your index. This is a great way to pass future practice tests, as they all share a question bank. It is also a great way to fail the real exam. This is also why I do not recommend taking more than three practice exams, diminishing returns will give you a false sense of security. Instead, use what you got wrong as a jumping off point for further research. Practice tests are also a great way to figure out how well you need to know each topic.
Practice exams will also get you familiar with how the GIAC exams work. I was new to GIAC and familiar with CompTIA, so I was not prepared for the idea that many questions would have many correct answers and one “good” answer. I also had to learn when to “skip” questions. You have a limited number of questions that you can skip and come back to later, and if you answer a question and submit it you will not be able to return to it. Reading the questions very carefully seems like a cliche, but it was a legitimate skill that I had to develop to prepare for the exam. I really do appreciate that with GIAC, there’s no substitute at any stage for study, practice, and applied effort.
Before scheduling the real exam, know that the practice exam is easier than the real exam, so you should be getting a score of 5–10 points higher than you need to. This actually varies between the different GIAC exams. I’ve seen many who took other SANS DFIR exams say that their practice exams were harder than their exam.
The GIAC Exam “Application”
When you’re purchasing your GREM exam, you will have to fill out an application and wait two days for approval before you can schedule or access your free practice exams. I don’t think anyone’s really gone into what to put on this, but I wouldn’t stress about it. I doubt they put too much weight into what your qualifications are, but they probably care about how you studied and what you’re bringing into the exam. When you’re filling out the application, be honest. Don’t be afraid to mention non-SANS certifications you already have, courses you’ve taken with them or others, your current position, the books you used to prepare for the exam, and what your index is based off of. You’ll probably be approved within a day or so.
Exam Regrets
My biggest regret is probably putting everything related to network-related behavioral analysis and script based malware till the last second. I was unprepared for this section, and though I passed the exam with an 81.3%, my score in these sections would have been much higher if I had done more practice instead of just reading related to this topic. I put too much emphasis on executable analysis even after figuring out that this was my weakest area. My recommendation is to focus on the weakest areas that you see in your practice tests before anything else.
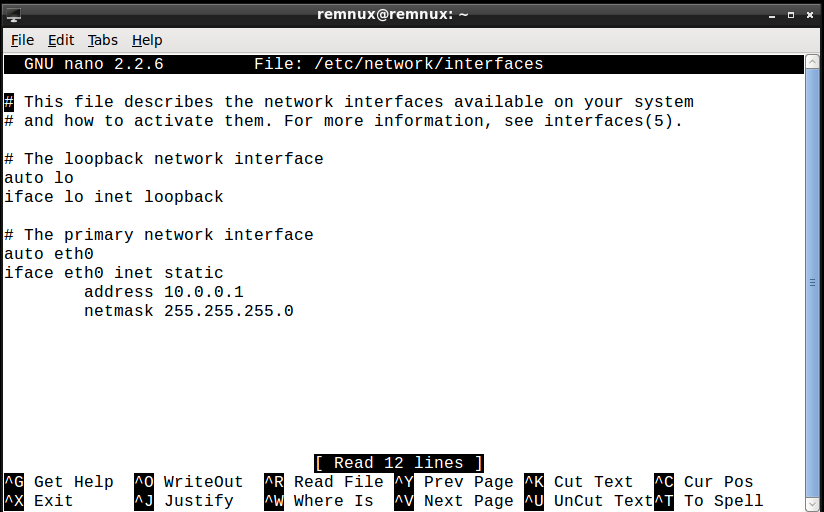
My Next Steps
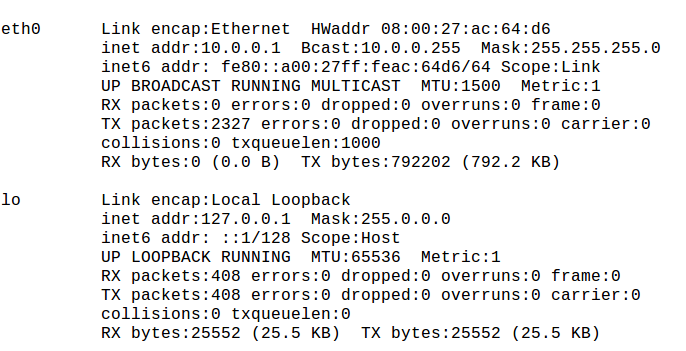
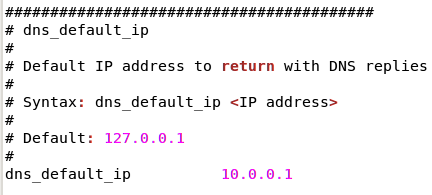
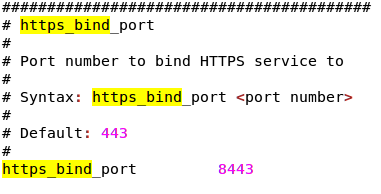
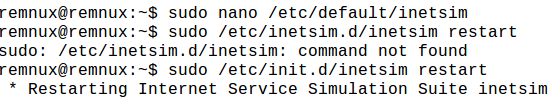
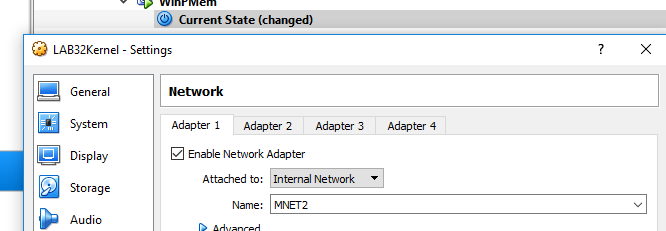
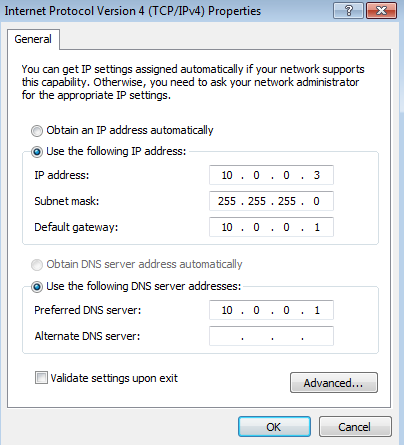
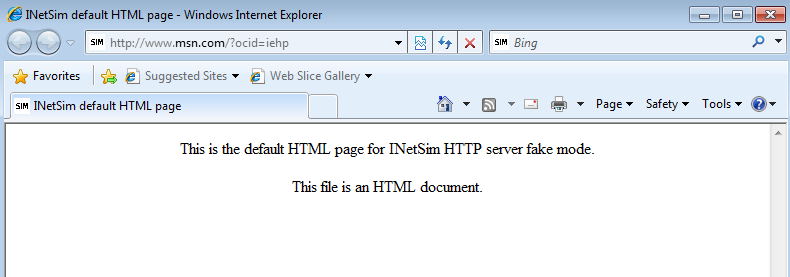
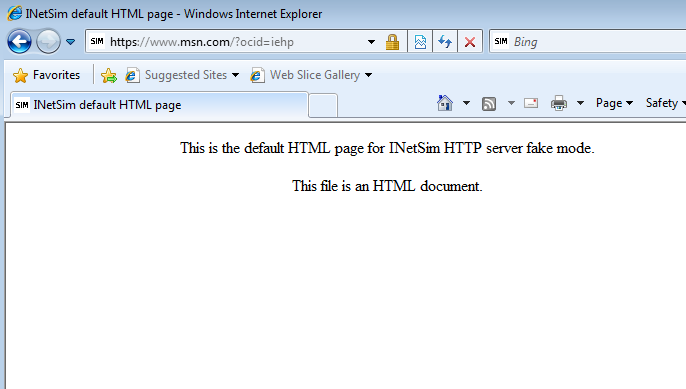
Memory forensics, network-related behavioral analysis, and kernel mode debugging are three things that I would like to learn more about. I decided to hit all of these in one go by analyzing rootkits. I’ll be posting an article soon on how to set up a lab to analyze Win32 rootkits, and another one where I analyze a kernel mode rootkit sample (probably Cutwail, subject to change) using behavioral analysis tools, network tools like INetSim, the kernel mode debugger WinDBG, and Volatility plugins for rootkit memory forensics.
I should also probably analyze some more document based javascript and VB macro samples to ensure that my understanding of the techniques used to analyze these types of malware is solid.